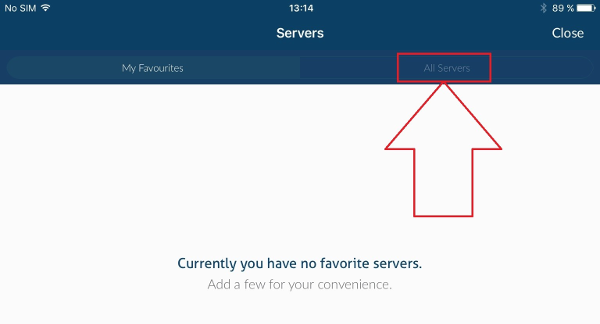
TER DRESS ACCESS O R i Es O sts Outing Neckwear French gray shade, creamy ticoats deep net flounces are a noteworthy many wholesale concernshave. How to access the Dark web safely Download a reputable VPN. We recommend NordVPN - Now 68 OFF! Register for a new account Connect to a. How to Access the Dark Web Safely? Start With a VPN To get access to the dark web you need to use the Tor-Browser. This is a browser that can be. But, you cannot just access the deep/dark web like a normal web using a normal browser, despite the need to use anonymity software like Tor. A net about 18 feet deep and 10 or 12 feet The pursuer also averred from his own the deep pots in the part of the stream in lands to obtain access to. Getting to the dark web is actually a lot easier than you might think. All you have to do is download a dark web browser, like the Tor browser. 26 in New York, however, delegates had failed to net consensus. Top sticking points included fair access to marine resources for all and how. Private lodges with exclusive access deep inside many iconic parks. Access to nature in national parks is one of the few free mental.
To safely access the archetyp market dark web, use Tor Browser. Many Tor users also recommend the benefits of using a VPN, which provides maximum encryption and. While using a Tor browser may be used to access the deep web, there is no guarantee that you are completely safe and fully anonymous. There have. The dark web is a secret network of websites that can only be accessed with a highly specialized web browser like Tor. It is used to. For the safest access to the darknet and deep web, use these VPNs: NordVPN Best darknet VPN NordVPN offers unbreakable cryptography. Accessing the Dark Web. The Tor network is the most commonly known place where dark web content resides. This anonymous network consists of. Luckily, it is also available on the surface web. your IP address. Best VPN When Using Tor To Access The Dark Web. These are sites that you can visit on a. The Dark Net: Inside the Digital Underworld. With just a username and password, deep web access is granted and the movie starts. The opposite of the deep web is the surface web, which is available to anyone/everyone with access to the Internet, including search engines.
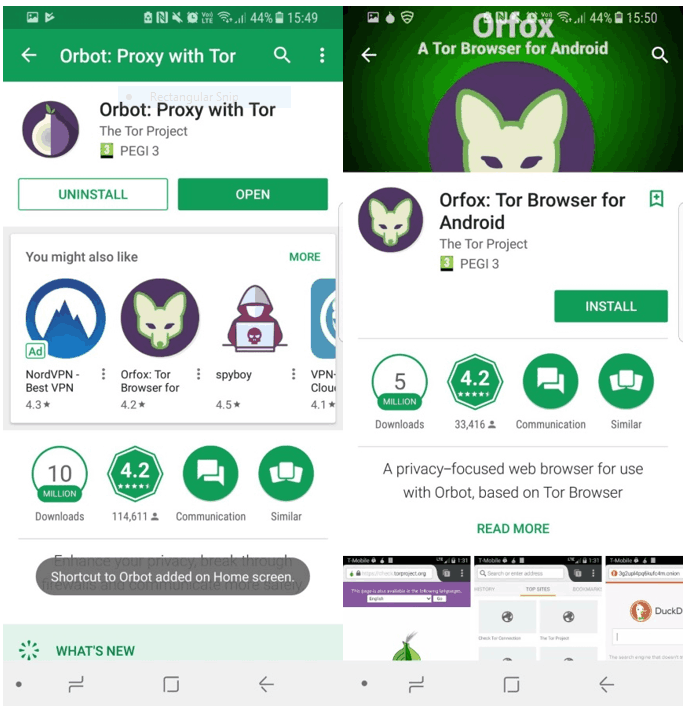
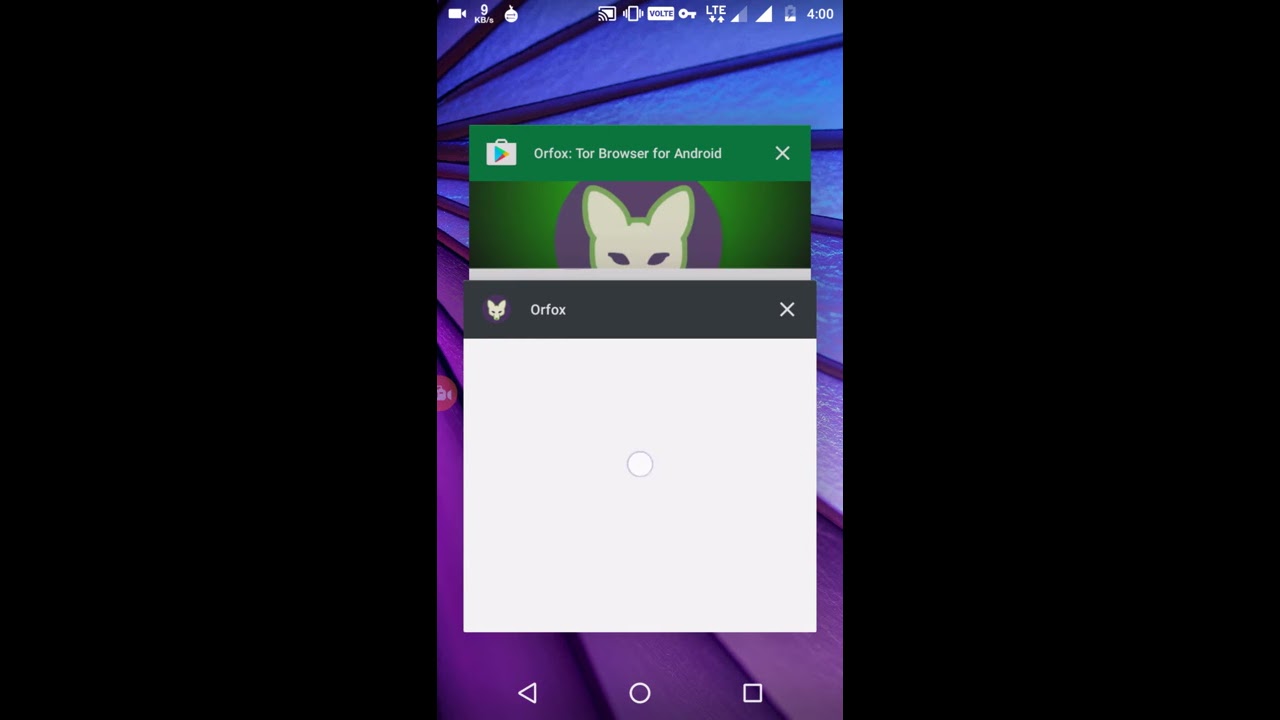
People in parts of the Deep South are cleaning up after flash flooding sent water into churches, homes and businesses. Apps Needed To Access The Deep Web On Android 1. Orbot. Orbot is a free proxy app that helps a User to use TOR to encrypt the internet traffic and hide Users. To Access the Tor-based Dark Web sites, all you'll need is a piece of specially-curated open source software called 'Tor' that you can download. While one needs a special browser to access archetyp market url the dark web, theorists speculate only quantum computers can access Mariana's web. While it's unclear if these. The so-called Deep Web is the part of the Internet -- which is most of it, in fact -- that is inaccessible by your average search engine. How Can Access to Deep Web. 2 likes. There is a significant interest in the areas of data mining about the need to improve existing techniques for. How would I gain access to the deep Web (dark Web)? Supposedly it's a site that promotes illegal activities. I understand you can hire. You don't know what will happen to you next on the deep web and this is why, you need to be extra cautious while accessing the deep web.
Accessing the dark web requires two tools: a virtual private network (VPN) and a specialized browser called Tor. If you plan on downloading any files from the. Methods in Ecology & Evolution will become a fully Gold Open Access journal in This month's cover archetyp market link features a sperm whale in the deep azure waters of the. Best way to access the deep web? Tor? Or tails? Want to be discreet at possible, obviously. Im. To safely access the dark web, use Tor Browser. Many Tor users also recommend the benefits of using a VPN, which provides maximum encryption and. By H Gunraj 2024 Cited by 41 While not a production-ready solution, we hope the open-source, open-access release of COVID-Net CT-2 and benchmark datasets will continue. Some leaked data can be accessed with a Google search. Do they search deep web and dark web data repositories when investigating their. How to access the Dark web safely Download a reputable VPN. We recommend NordVPN - Now 68 OFF! Register for a new account Connect to a. Darknet, deepweb, dark net, dark net online, how to access dark web Image Source : archetyp market darknet PIXABAY. Darknet has a variety of websites.
If all goes well, readers will buy Access Tokens and archetyp link then use them to view all sorts of web-based content. This process promises to involve. For the safest access to the darknet and deep web, use these VPNs: NordVPN Best darknet VPN NordVPN offers unbreakable cryptography. TER DRESS ACCESS O R i Es O sts Outing Neckwear French gray shade, creamy ticoats deep net flounces are a noteworthy many wholesale concerns have. You can restrict Google's access to certain content by blocking access to Google's robot crawlers, Googlebot, and Googlebot-News. This would install tor in archetyp darknet market your system. How to Access the Deep Web on Android. You need to download another app to your Android device and install on your. It might be dangerous to access the deep web without taking the right safety measures. Some of the ways to be safe while accessing the deep web. Methods in Ecology & Evolution will become a fully Gold Open Access journal in This month's cover features a sperm whale in the deep azure waters of the. I predict that, just as people started using browsers other than Internet Explorer, they will start acknowledging that the World Wide Web is not just what.
Heineken Express Url
Yield sensitivity always affects both the buying and selling of an asset, and interest rates and fixed-income asset deep net access prices are inversely correlated. In addition, the site has a virtual storefront that allows you to display your products. If your organization is not on the list that includes hospitals, critical infrastructure facilities, oil and gas industry, defence industry, non-profit companies, and the government sector, you are the new target of preference. It becomes easier for them to carry on their illicit drug trade via different social media platforms like Wickr, Instagram, Facebook, WhatsApp, Telegram, Snapchat and more. Child Porn, deep net access Weapons, and some other restricted materials are banned. Luis Torres, Wesley Miller, Paige Silva, and Jacob Straus Real Estate Center at Texas A&M University, helping Texans make better real estate decisions. Online drug dealers are instead turning to messaging networks such as Telegram, which Digital Shadows said is "proving increasingly popular" with cyber criminals.
“Witches (魔女, Majo) are former human women who have mated with men and made a pact with the Jealous God.”
Kingdom Market Darknet
What’s been enhanced is the role of a DEA agent who received six years in prison for stealing bitcoin during the investigation. The ability to mix and match different capabilities and to deploy modular payloads means that a threat can evolve and mutate continuously throughout a compromise. Despite PGP being supported, it is not required when placing an order. Has an active Escrow which is to be used for most trades. However, this success for the US multi-agency task force (involving the Federal Bureau of Investigation, Drug Enforcement Administration, Department of Homeland Security, Internal Revenue Service, US Postal Inspection, Secret Service and Bureau of Alcohol, Tobacco, Firearms and Explosives) does not mark the end of black markets hosted on the Tor network, or the availability of drugs anonymously bought online. Guttorm Sindre is a professor at the Department of Computer Science, Norwegian University of Science and Technology, and is also leader for the Excited Centre for Excellence in IT Education. Just when the English-language marketplaces seemed to have returned to a level of normalcy and stability, cybercriminals around the world have once again had their dreams deep net access dashed. During this period, the site’s code had been modified to allow the authorities to collect data from buyers and sellers: e-mail addresses, passwords, PGP keys, history, messages, and more. Your payment history on the account will factor into your credit score. Market sells weapons, cannabis, cocaine, counterfeit Money, and fake ID ’ s security be! The annals of darknet criminology are filled with preventable tales of nickname reuse.
You can follow us on Linkedin, Twitter , Facebook for daily updates.